APIs now underpin many digital strategies, helping companies share data with internal stakeholders and empowering brand-new API-as-as-products to form. APIs power event-driven microservices architectures and enable the composable enterprise to take shape. But although web APIs may be the lingua franca of modern connected technologies, they present novel challenges. Because as the value of API-based connections rises, so do new threats.
In recent years, we've seen an alarming increase in API attacks. For example, Salt Security discovered an impressive 681% rise in API attack traffic in mid-2022. Many APIs lack the proper authorization controls, leaving weak HTTP methods open for exploits by hackers, who often exfiltrate mass amounts of data undetected. And as the number of APIs increases, sprawl concerns are beginning to emerge, along with shadow or zombie endpoints. There is also the urgency to protect sensitive data and comply with new global data regulations.
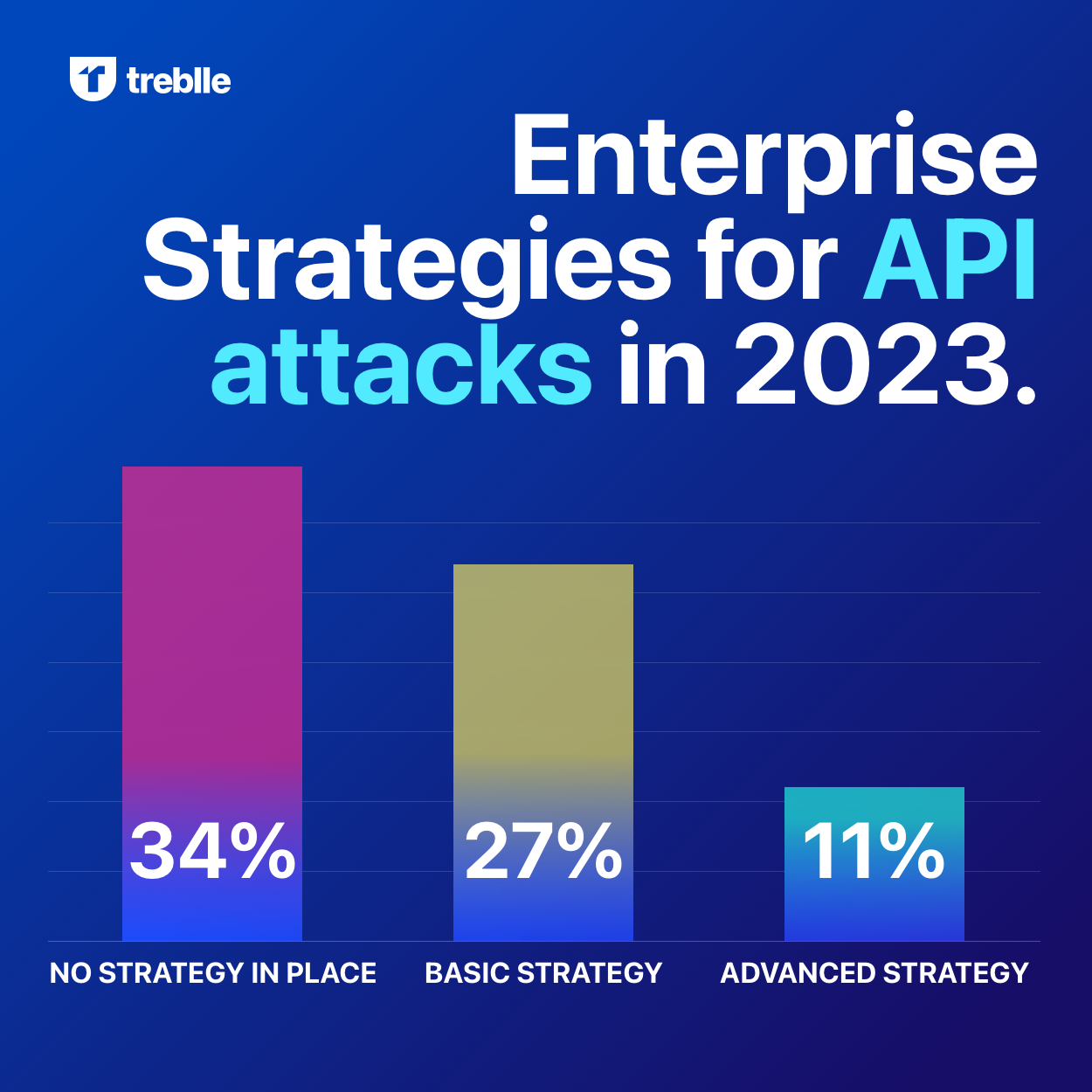
Due to these concerns and others, there is a newfound urgency to protect APIs from escalating threats. As a result, in 2023, API security is becoming a top concern for cybersecurity professionals at large. Below, we'll outline some of the most common API vulnerabilities that persist today and zoom in on methods to mitigate them. We'll consider what's to come in API security within this year and beyond, and outline some best practices to keep your API strategies safe from abuse.
Top API Security Risks
There are many potential security risks associated with using and hosting APIs. First and foremost, if improperly configured, APIs can easily fall victim to weak access control. In fact, OWASP's API Security Top 10 places Broken Object Level Authorization (BOLA) as the #1 threat facing modern APIs. BOLA means that authorization controls are nonexistent or implemented improperly — this could, for example, allow a hacker to switch out a unique identifier in the HTTP call to access resources from another account, or even manipulate data. Unauthorized access to sensitive data goes against the rule of least privilege and leads to data overexposure.
Furthermore, many APIs have weak authentication methods in place. Some are still using HTTP Basic Authentication, but most have graduated to adopting API keys associated with each developer or app account. Even then, API keys have been proven to be insufficient for appropriately delegating identity. Furthermore, API keys for cloud-native tools can easily be stolen or accidentally left exposed in public repositories.
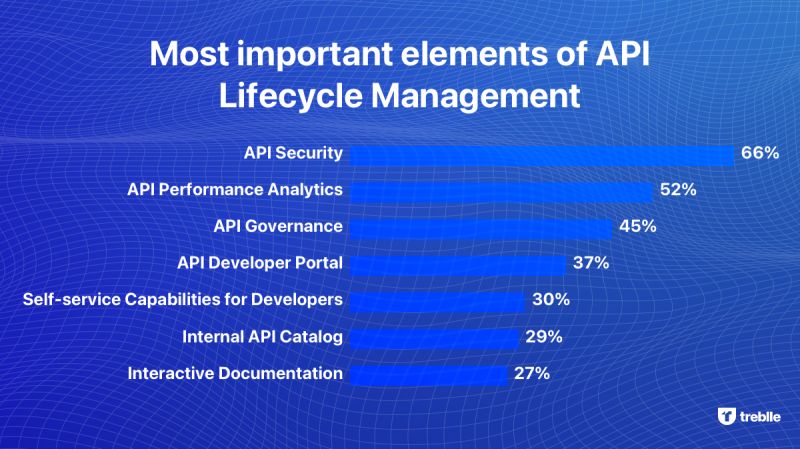
Too often, as the number of APIs balloons within an organization, it's easy to lose track of these integration points, let alone track them all continuously. And what's more, is that it can be challenging to distinguish regular API traffic from malicious bots or hackers performing reconnaissance to identify gaps. Insufficient logging and monitoring thus present a potential risk, since it leaves APIs unattended and more opaque when addressing misuse.
Strategies for Securing APIs
So, knowing the above threats, how can organizations ensure their APIs are secure? Well, arguably the first step with any cybersecurity effort is to understand your surface area. It's a good idea to audit the number of active APIs within your organization and keep track of new integrations in a common catalog. Doing so not only enhances the discoverability of internal services but helps ensure they aren't forgotten. Seeing the greater software lifecycle and having a deprecation policy in place from the start can also ensure APIs don't ever devolve into unmaintained shadow IT.
Next, it's good practice to implement advanced authentication and authorization policies. Applications utilizing API connections should require multi-factor authentication. Furthermore, it's a recommended practice to go beyond HTTP Basic Authentication and API keys to use open standards like OAuth and OpenID Connect. This will ensure that API requesters, whether they are humans, devices, or servers, are properly authorized and that their identity is traced throughout a zero-trust software ecosystem. Most secure APIs adopt an API gateway and use management solutions that encrypt data in transit and rate limit use — all helpful vectors to reduce threat.
It's also encouraged to adopt internal style guides and policies to ensure APIs are built consistently. For example, aligning specification-driven development with a standard like OpenAPI Specification can encourage governance around API-first development. All in all, API project managers should seek to consistently identify gaps in their security culture and upskill team members on the dangers of overexposure when building integrations between components.
Insecure APIs Hurt Business
APIs aren't just for technology companies anymore. As more and more organizations become digital-first enterprises, they will continue to rely on APIs to outsource scalable serverless capabilities and to avoid reinventing the wheel for common functionalities. APIs also drive many modern DevOps initiatives, helping cloud-native architectures thrive. Yet, this reliance can be costly to the business if APIs aren't adequately secured.
One report estimated that in 2022, US companies faced $12-23 billion in losses as a result of compromises linked to web APIs. One such recent hack was the Optus API breach in which black hats demanded a $1 million ransom. Or, take the recent T-Mobile hack, in which a leaky API was leveraged to steal the records of 37 million customers. These API breaches are significant not only because they hurt the balance sheet but also because they diminish brand reputation and consumer faith.
As investment into APIs increases, so will the rate of new vulnerabilities associated with API initiatives. Looking to the future, IT will have to grapple with new threats surrounding emerging API styles like GraphQL. Institutions in the finance and healthcare sectors will especially be under pressure to open data securely to comply with upcoming regulations.
All these reasons underscore the need for intelligent API security forethought that treats all services, whether internal, partner-facing, or externalized products, from a zero-trust angle. By taking some of the precautions above, organizations can leverage all the benefits of an API strategy while reducing many — if not all — of the threats.






